Major refactor to blue-build to allow more complex builds
This commit is contained in:
parent
01259cef7b
commit
fb2297478c
15 changed files with 215 additions and 500 deletions
1
.github/CODEOWNERS
vendored
Normal file
1
.github/CODEOWNERS
vendored
Normal file
|
|
@ -0,0 +1 @@
|
|||
* @xynydev @fiftydinar
|
||||
6
.github/dependabot.yml
vendored
Normal file
6
.github/dependabot.yml
vendored
Normal file
|
|
@ -0,0 +1,6 @@
|
|||
version: 2
|
||||
updates:
|
||||
- package-ecosystem: "github-actions"
|
||||
directory: "/"
|
||||
schedule:
|
||||
interval: "daily"
|
||||
261
.github/workflows/bazzite-build-gnome.yml
vendored
261
.github/workflows/bazzite-build-gnome.yml
vendored
|
|
@ -1,261 +0,0 @@
|
|||
---
|
||||
name: bazzite-build-gnome
|
||||
on:
|
||||
pull_request:
|
||||
branches:
|
||||
- main
|
||||
schedule:
|
||||
- cron: '05 05 * * *' # 05:05am UTC everyday
|
||||
push:
|
||||
branches:
|
||||
- main
|
||||
paths-ignore:
|
||||
- '**/README.md'
|
||||
workflow_dispatch:
|
||||
|
||||
env:
|
||||
MY_IMAGE_NAME: "bazzite-badblocks-gnome" # the name of the image produced by this build
|
||||
MY_IMAGE_DESC: "badblocks's custom bazzite-gnome build"
|
||||
IMAGE_REGISTRY: "ghcr.io/${{ github.repository_owner }}" # do not edit
|
||||
|
||||
jobs:
|
||||
read_groups:
|
||||
name: Read RPM groups from build.sh
|
||||
runs-on: ubuntu-latest
|
||||
container: fedora:latest
|
||||
outputs:
|
||||
group_pkgs: ${{ steps.extract_groups.outputs.result }}
|
||||
steps:
|
||||
- name: Checkout repository
|
||||
uses: actions/checkout@v4
|
||||
|
||||
- name: Extract quoted groups
|
||||
id: extract_groups
|
||||
shell: bash
|
||||
run: |
|
||||
# Find the rpm-ostree groupinstall lines and extract quoted strings
|
||||
VALUE=$(grep '^rpm-ostree groupinstall' build.sh | grep -o '"[^"]*"' | tr '\n' ' ')
|
||||
echo "Extracted VALUE: $VALUE"
|
||||
|
||||
if [ -z "$VALUE" ]; then
|
||||
echo "No groups found in build.sh"
|
||||
echo "result=" >> "$GITHUB_OUTPUT"
|
||||
exit 0
|
||||
fi
|
||||
|
||||
# Initialize an empty array
|
||||
declare -a GROUP_ARRAY
|
||||
|
||||
# Use read with a custom delimiter to split the input string
|
||||
while IFS='"' read -ra parts; do
|
||||
for part in "${parts[@]}"; do
|
||||
# Trim leading and trailing spaces and check if the part is not empty
|
||||
trimmed=$(echo "$part" | xargs)
|
||||
if [[ -n "$trimmed" ]]; then
|
||||
GROUP_ARRAY+=("$trimmed")
|
||||
fi
|
||||
done
|
||||
done <<< "$VALUE"
|
||||
echo "Raw Array without double-quotes: ${GROUP_ARRAY[@]}"
|
||||
|
||||
IS_DNF5=$(dnf --version | { grep -sc dnf5 || test $? = 1; })
|
||||
echo "IS_DNF5: $IS_DNF5 (dnf4 = 0, else dnf5)"
|
||||
echo -n result= >> "$GITHUB_OUTPUT"
|
||||
for GROUP_E in "${GROUP_ARRAY[@]}"; do
|
||||
echo "Getting pkgs for group: $GROUP_E"
|
||||
if [ "$IS_DNF5" -ne 0 ]; then
|
||||
#dnf5
|
||||
echo -n $(dnf group info "$GROUP_E" 2>&1 | grep -E "packages|^[[:space:]]*:" | cut -d: -f2 | tr -s ' ' | tr -d '\n' | sed 's/^ //; s/ $//') >> "$GITHUB_OUTPUT"
|
||||
else
|
||||
#dnf4
|
||||
echo -n $(dnf group info "$GROUP_E" 2>&1 | grep -v : | tr -d '\n' | tr -s ' ' | cut -c2-) >> "$GITHUB_OUTPUT"
|
||||
fi
|
||||
echo -n " " >> "$GITHUB_OUTPUT"
|
||||
done
|
||||
|
||||
#run: |
|
||||
# Find the rpm-ostree groupinstall lines and extract quoted strings
|
||||
#VALUE=$(grep '^rpm-ostree groupinstall' build.sh | grep -o '"[^"]*"' | tr '\n' ' ')
|
||||
#GROUPS=( $VALUE )
|
||||
#IS_DNF5=$(dnf --version | grep -c dnf5)
|
||||
# for GROUP in "${GROUPS[@]}"; do
|
||||
# if [ "$IS_DNF5" -ne 0 ]; then
|
||||
# #dnf5
|
||||
# echo $GROUP
|
||||
# else
|
||||
# #dnf4
|
||||
# echo $GROUP
|
||||
# fi
|
||||
# done
|
||||
#echo "result=$VALUE" >> "$GITHUB_OUTPUT"
|
||||
|
||||
# get_pkg_lists:
|
||||
# name: Retrieve group package lists from fedora:latest dnf group list
|
||||
# runs-on: ubuntu-latest
|
||||
# container: fedora:latest
|
||||
# needs: read_groups
|
||||
# outputs:
|
||||
# GROUP_PKGS: ${{ steps.get_pkg_list.outputs.result }}
|
||||
# steps:
|
||||
# - name: Get package lists from specified groups
|
||||
# shell: bash
|
||||
# run: |
|
||||
# GROUPS=( ${{ needs.read_groups.outputs.groups }} )
|
||||
# IS_DNF5=$(dnf --version | grep -c dnf5)
|
||||
# for GROUP in "${GROUPS[@]}"; do
|
||||
# echo $(dnf group info "$GROUP")
|
||||
# if [ "$IS_DNF5" -ne 0 ]; then
|
||||
# #dnf5
|
||||
# echo "result=$(dnf group info "$GROUP" 2>&1 | grep -E "packages|^[[:space:]]*:" | cut -d: -f2 | tr -s ' ' | tr -d '\n' | sed 's/^ //; s/ $//')" >> "$GITHUB_OUTPUT"
|
||||
# else
|
||||
# #dnf4
|
||||
# echo "result=$(dnf group info "$GROUP" 2>&1 | grep -v : | tr -d '\n' | tr -s ' ' | cut -c2-)" >> "$GITHUB_OUTPUT"
|
||||
# fi
|
||||
# done
|
||||
|
||||
build_push:
|
||||
name: Build and push image
|
||||
runs-on: ubuntu-24.04
|
||||
needs: read_groups
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
packages: write
|
||||
id-token: write
|
||||
|
||||
steps:
|
||||
# Checkout push-to-registry action GitHub repository
|
||||
- name: Checkout Push to Registry action
|
||||
uses: actions/checkout@v4
|
||||
|
||||
- name: Maximize build space
|
||||
uses: ublue-os/remove-unwanted-software@v7
|
||||
|
||||
- name: Replace groupinstall <groups> with install <pkgs> in build.sh
|
||||
run: |
|
||||
sed -i "s/^rpm-ostree groupinstall.*/rpm-ostree install ${{ needs.read_groups.outputs.group_pkgs }}/" build.sh
|
||||
|
||||
- name: Generate tags
|
||||
id: generate-tags
|
||||
shell: bash
|
||||
run: |
|
||||
# Generate a timestamp for creating an image version history
|
||||
TIMESTAMP="$(date +%Y%m%d)"
|
||||
COMMIT_TAGS=()
|
||||
BUILD_TAGS=()
|
||||
|
||||
# Have tags for tracking builds during pull request
|
||||
SHA_SHORT="${GITHUB_SHA::7}"
|
||||
COMMIT_TAGS+=("pr-${{ github.event.number }}")
|
||||
COMMIT_TAGS+=("${SHA_SHORT}")
|
||||
|
||||
# Append matching timestamp tags to keep a version history
|
||||
for TAG in "${BUILD_TAGS[@]}"; do
|
||||
BUILD_TAGS+=("${TAG}-${TIMESTAMP}")
|
||||
done
|
||||
|
||||
BUILD_TAGS+=("${TIMESTAMP}")
|
||||
if [[ ${{ github.ref_name }} == "unstable" ]]; then
|
||||
BUILD_TAGS+=("unstable")
|
||||
SOURCE_VERSION="unstable"
|
||||
elif [[ ${{ github.ref_name }} == "testing" ]]; then
|
||||
BUILD_TAGS+=("testing")
|
||||
SOURCE_VERSION="testing"
|
||||
else
|
||||
BUILD_TAGS+=("latest" "stable")
|
||||
SOURCE_VERSION="latest"
|
||||
fi
|
||||
|
||||
if [[ "${{ github.event_name }}" == "pull_request" ]]; then
|
||||
echo "Generated the following commit tags: "
|
||||
for TAG in "${COMMIT_TAGS[@]}"; do
|
||||
echo "${TAG}"
|
||||
done
|
||||
|
||||
alias_tags=("${COMMIT_TAGS[@]}")
|
||||
else
|
||||
alias_tags=("${BUILD_TAGS[@]}")
|
||||
fi
|
||||
|
||||
echo "Generated the following build tags: "
|
||||
for TAG in "${BUILD_TAGS[@]}"; do
|
||||
echo "${TAG}"
|
||||
done
|
||||
|
||||
echo "alias_tags=${alias_tags[*]}" >> $GITHUB_OUTPUT
|
||||
|
||||
# Build metadata
|
||||
- name: Image Metadata
|
||||
uses: docker/metadata-action@v5
|
||||
id: meta
|
||||
with:
|
||||
images: |
|
||||
${{ env.MY_IMAGE_NAME }}
|
||||
|
||||
labels: |
|
||||
io.artifacthub.package.readme-url=https://raw.githubusercontent.com/${{ github.repository }}/main/README.md
|
||||
org.opencontainers.image.description=${{ env.MY_IMAGE_DESC }}
|
||||
org.opencontainers.image.title=${{ env.MY_IMAGE_NAME }}
|
||||
|
||||
# Build image using Buildah action
|
||||
- name: Build Image
|
||||
id: build_image
|
||||
uses: redhat-actions/buildah-build@v2
|
||||
with:
|
||||
containerfiles: |
|
||||
./Containerfile
|
||||
# Postfix image name with -custom to make it a little more descriptive
|
||||
# Syntax: https://docs.github.com/en/actions/learn-github-actions/expressions#format
|
||||
image: ${{ env.MY_IMAGE_NAME }}
|
||||
tags: |
|
||||
${{ steps.generate-tags.outputs.alias_tags }}
|
||||
labels: ${{ steps.meta.outputs.labels }}
|
||||
oci: false
|
||||
|
||||
# Workaround bug where capital letters in your GitHub username make it impossible to push to GHCR.
|
||||
# https://github.com/macbre/push-to-ghcr/issues/12
|
||||
- name: Lowercase Registry
|
||||
id: registry_case
|
||||
uses: ASzc/change-string-case-action@v6
|
||||
with:
|
||||
string: ${{ env.IMAGE_REGISTRY }}
|
||||
|
||||
- name: Login to GitHub Container Registry
|
||||
uses: docker/login-action@v3
|
||||
with:
|
||||
registry: ghcr.io
|
||||
username: ${{ github.actor }}
|
||||
password: ${{ secrets.GITHUB_TOKEN }}
|
||||
|
||||
- name: Push Image to GHCR
|
||||
uses: redhat-actions/push-to-registry@v2
|
||||
id: push
|
||||
env:
|
||||
REGISTRY_USER: ${{ github.actor }}
|
||||
REGISTRY_PASSWORD: ${{ github.token }}
|
||||
with:
|
||||
image: ${{ steps.build_image.outputs.image }}
|
||||
tags: ${{ steps.build_image.outputs.tags }}
|
||||
registry: ${{ steps.registry_case.outputs.lowercase }}
|
||||
username: ${{ env.REGISTRY_USER }}
|
||||
password: ${{ env.REGISTRY_PASSWORD }}
|
||||
extra-args: |
|
||||
--disable-content-trust
|
||||
|
||||
# This section is optional and only needs to be enabled if you plan on distributing
|
||||
# your project for others to consume. You will need to create a public and private key
|
||||
# using Cosign and save the private key as a repository secret in Github for this workflow
|
||||
# to consume. For more details, review the image signing section of the README.
|
||||
|
||||
# Sign container
|
||||
- uses: sigstore/cosign-installer@v3.5.0
|
||||
if: github.event_name != 'pull_request'
|
||||
|
||||
- name: Sign container image
|
||||
if: github.event_name != 'pull_request'
|
||||
run: |
|
||||
cosign sign -y --key env://COSIGN_PRIVATE_KEY ${{ steps.registry_case.outputs.lowercase }}/${{ steps.build_image.outputs.image }}@${TAGS}
|
||||
env:
|
||||
TAGS: ${{ steps.push.outputs.digest }}
|
||||
COSIGN_EXPERIMENTAL: false
|
||||
COSIGN_PRIVATE_KEY: ${{ secrets.SIGNING_SECRET }}
|
||||
36
.github/workflows/build.yml
vendored
Normal file
36
.github/workflows/build.yml
vendored
Normal file
|
|
@ -0,0 +1,36 @@
|
|||
name: bluebuild
|
||||
on:
|
||||
schedule:
|
||||
- cron: "00 07 * * *" # build at 07:00 UTC every day
|
||||
# (1:20 hours after last ublue images start building)
|
||||
push:
|
||||
paths-ignore: # don't rebuild if only documentation has changed
|
||||
- "**.md"
|
||||
|
||||
pull_request:
|
||||
workflow_dispatch: # allow manually triggering builds
|
||||
jobs:
|
||||
bluebuild:
|
||||
name: Build Custom Image
|
||||
runs-on: ubuntu-latest
|
||||
permissions:
|
||||
contents: read
|
||||
packages: write
|
||||
id-token: write
|
||||
strategy:
|
||||
fail-fast: false # stop GH from cancelling all matrix builds if one fails
|
||||
matrix:
|
||||
recipe:
|
||||
- recipe.yml
|
||||
steps:
|
||||
# the build is fully handled by the reusable github action
|
||||
- name: Build Custom Image
|
||||
uses: blue-build/github-action@v1.7
|
||||
with:
|
||||
recipe: ${{ matrix.recipe }}
|
||||
cosign_private_key: ${{ secrets.SIGNING_SECRET }}
|
||||
registry_token: ${{ github.token }}
|
||||
pr_event_number: ${{ github.event.number }}
|
||||
|
||||
# enabled by default, disable if your image is small and you want faster builds
|
||||
maximize_build_space: false
|
||||
3
.gitignore
vendored
Normal file
3
.gitignore
vendored
Normal file
|
|
@ -0,0 +1,3 @@
|
|||
cosign.key
|
||||
cosign.private
|
||||
/Containerfile
|
||||
|
|
@ -1,59 +0,0 @@
|
|||
## 1. BUILD ARGS
|
||||
# These allow changing the produced image by passing different build args to adjust
|
||||
# the source from which your image is built.
|
||||
# Build args can be provided on the commandline when building locally with:
|
||||
# podman build -f Containerfile --build-arg FEDORA_VERSION=40 -t local-image
|
||||
|
||||
# SOURCE_IMAGE arg can be anything from ublue upstream which matches your desired version:
|
||||
# See list here: https://github.com/orgs/ublue-os/packages?repo_name=main
|
||||
# - "silverblue"
|
||||
# - "kinoite"
|
||||
# - "sericea"
|
||||
# - "onyx"
|
||||
# - "lazurite"
|
||||
# - "vauxite"
|
||||
# - "base"
|
||||
#
|
||||
# "aurora", "bazzite", "bluefin" or "ucore" may also be used but have different suffixes.
|
||||
ARG SOURCE_IMAGE="bazzite"
|
||||
|
||||
## SOURCE_SUFFIX arg should include a hyphen and the appropriate suffix name
|
||||
# These examples all work for silverblue/kinoite/sericea/onyx/lazurite/vauxite/base
|
||||
# - "-main"
|
||||
# - "-nvidia"
|
||||
# - "-asus"
|
||||
# - "-asus-nvidia"
|
||||
# - "-surface"
|
||||
# - "-surface-nvidia"
|
||||
#
|
||||
# aurora, bazzite and bluefin each have unique suffixes. Please check the specific image.
|
||||
# ucore has the following possible suffixes
|
||||
# - stable
|
||||
# - stable-nvidia
|
||||
# - stable-zfs
|
||||
# - stable-nvidia-zfs
|
||||
# - (and the above with testing rather than stable)
|
||||
ARG SOURCE_SUFFIX="-gnome"
|
||||
|
||||
## FEDORA_VERSION arg must be a version built by ublue
|
||||
ARG FEDORA_VERSION="latest"
|
||||
|
||||
|
||||
### 2. SOURCE IMAGE
|
||||
## this is a standard Containerfile FROM using the build ARGs above to select the right upstream image
|
||||
FROM ghcr.io/ublue-os/${SOURCE_IMAGE}${SOURCE_SUFFIX}:${FEDORA_VERSION}
|
||||
|
||||
|
||||
### 3. MODIFICATIONS
|
||||
## make modifications desired in your image and install packages by modifying the build.sh script
|
||||
## the following RUN directive does all the things required to run "build.sh" as recommended.
|
||||
|
||||
COPY build.sh /tmp/build.sh
|
||||
|
||||
RUN mkdir -p /var/lib/alternatives && \
|
||||
/tmp/build.sh && \
|
||||
ostree container commit
|
||||
## NOTES:
|
||||
# - /var/lib/alternatives is required to prevent failure with some RPM installs
|
||||
# - All RUN commands must end with ostree container commit
|
||||
# see: https://coreos.github.io/rpm-ostree/container/#using-ostree-container-commit
|
||||
|
|
@ -1,82 +0,0 @@
|
|||
# image-template
|
||||
|
||||
# Purpose
|
||||
|
||||
This repository is meant to be a template for building your own custom Universal Blue image. This template is the recommended way to make customizations to any image published by the Universal Blue Project:
|
||||
- [Aurora](https://getaurora.dev/)
|
||||
- [Bazzite](https://bazzite.gg/)
|
||||
- [Bluefin](https://projectbluefin.io/)
|
||||
- [uCore](https://projectucore.io/)
|
||||
- [main](https://github.com/ublue-os/main/)
|
||||
- [hwe](https://github.com/ublue-os/hwe/)
|
||||
|
||||
This template includes a Containerfile and a Github workflow for building the container image. As soon as the workflow is enabled in your repository, it will build the container image and push it to the Github Container Registry.
|
||||
|
||||
# Prerequisites
|
||||
|
||||
Working knowledge in the following topics:
|
||||
|
||||
- Containers
|
||||
- https://www.youtube.com/watch?v=SnSH8Ht3MIc
|
||||
- https://www.mankier.com/5/Containerfile
|
||||
- rpm-ostree
|
||||
- https://coreos.github.io/rpm-ostree/container/
|
||||
- Fedora Silverblue (and other Fedora Atomic variants)
|
||||
- https://docs.fedoraproject.org/en-US/fedora-silverblue/
|
||||
- Github Workflows
|
||||
- https://docs.github.com/en/actions/using-workflows
|
||||
|
||||
# How to Use
|
||||
|
||||
## Template
|
||||
|
||||
Select `Use this Template` and create a new repository from it. To enable the workflows, you may need to go the `Actions` tab of the new repository and click to enable workflows.
|
||||
|
||||
## Containerfile
|
||||
|
||||
This file defines the operations used to customize the selected image. It contains examples of possible modifications, including how to:
|
||||
- change the upstream from which the custom image is derived
|
||||
- add additional RPM packages
|
||||
- add binaries as a layer from other images
|
||||
- modify system files (like /etc/systemd/system.conf)
|
||||
|
||||
## Workflows
|
||||
|
||||
### build.yml
|
||||
|
||||
This workflow creates your custom OCI image and publishes it to the Github Container Registry (GHCR).
|
||||
|
||||
#### Container Signing
|
||||
|
||||
Container signing is important for end-user security and is enabled on all Universal Blue images. It is recommended you set this up, and by default the image builds *will fail* if you don't.
|
||||
|
||||
This provides users a method of verifying the image.
|
||||
|
||||
1. Install the [cosign CLI tool](https://edu.chainguard.dev/open-source/sigstore/cosign/how-to-install-cosign/#installing-cosign-with-the-cosign-binary)
|
||||
|
||||
2. Run inside your repo folder:
|
||||
|
||||
```bash
|
||||
cosign generate-key-pair
|
||||
```
|
||||
|
||||
|
||||
- Do NOT put in a password when it asks you to, just press enter. The signing key will be used in GitHub Actions and will not work if it is encrypted.
|
||||
|
||||
> [!WARNING]
|
||||
> Be careful to *never* accidentally commit `cosign.key` into your git repo.
|
||||
|
||||
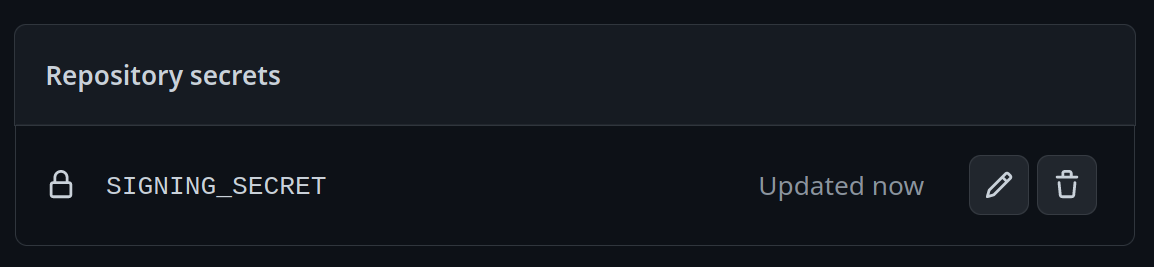
3. Add the private key to GitHub
|
||||
|
||||
- This can also be done manually. Go to your repository settings, under Secrets and Variables -> Actions
|
||||
|
||||
Add a new secret and name it `SIGNING_SECRET`, then paste the contents of `cosign.key` into the secret and save it. Make sure it's the .key file and not the .pub file. Once done, it should look like this:
|
||||
|
||||
|
||||
- (CLI instructions) If you have the `github-cli` installed, run:
|
||||
|
||||
```bash
|
||||
gh secret set SIGNING_SECRET < cosign.key
|
||||
```
|
||||
|
||||
4. Commit the `cosign.pub` file into your git repository
|
||||
44
README.md
44
README.md
|
|
@ -1,7 +1,43 @@
|
|||
# How to Use
|
||||
# ublue-custom [](https://github.com/badbl0cks/ublue-custom/actions/workflows/build.yml)
|
||||
|
||||
`rpm-ostree rebase ostree-image-signed:docker://ghcr.io/badbl0cks/bazzite-badblocks-kde`
|
||||
See the [BlueBuild docs](https://blue-build.org/how-to/setup/) for quick setup instructions for setting up your own repository based on this template.
|
||||
|
||||
or
|
||||
After setup, it is recommended you update this README to describe your custom image.
|
||||
|
||||
`rpm-ostree rebase ostree-image-signed:docker://ghcr.io/badbl0cks/bazzite-badblocks-gnome`
|
||||
## Installation
|
||||
|
||||
> **Warning**
|
||||
> [This is an experimental feature](https://www.fedoraproject.org/wiki/Changes/OstreeNativeContainerStable), try at your own discretion.
|
||||
|
||||
To rebase an existing atomic Fedora installation to the latest build:
|
||||
|
||||
- First rebase to the unsigned image, to get the proper signing keys and policies installed:
|
||||
```
|
||||
rpm-ostree rebase ostree-unverified-registry:ghcr.io/badbl0cks/ublue-custom:latest
|
||||
```
|
||||
- Reboot to complete the rebase:
|
||||
```
|
||||
systemctl reboot
|
||||
```
|
||||
- Then rebase to the signed image, like so:
|
||||
```
|
||||
rpm-ostree rebase ostree-image-signed:docker://ghcr.io/badbl0cks/ublue-custom:latest
|
||||
```
|
||||
- Reboot again to complete the installation
|
||||
```
|
||||
systemctl reboot
|
||||
```
|
||||
|
||||
The `latest` tag will automatically point to the latest build. That build will still always use the Fedora version specified in `recipe.yml`, so you won't get accidentally updated to the next major version.
|
||||
|
||||
## ISO
|
||||
|
||||
If build on Fedora Atomic, you can generate an offline ISO with the instructions available [here](https://blue-build.org/learn/universal-blue/#fresh-install-from-an-iso). These ISOs cannot unfortunately be distributed on GitHub for free due to large sizes, so for public projects something else has to be used for hosting.
|
||||
|
||||
## Verification
|
||||
|
||||
These images are signed with [Sigstore](https://www.sigstore.dev/)'s [cosign](https://github.com/sigstore/cosign). You can verify the signature by downloading the `cosign.pub` file from this repo and running the following command:
|
||||
|
||||
```bash
|
||||
cosign verify --key cosign.pub ghcr.io/badbl0cks/ublue-custom
|
||||
```
|
||||
|
|
|
|||
94
build.sh
94
build.sh
|
|
@ -1,94 +0,0 @@
|
|||
#!/bin/sh
|
||||
|
||||
set -oex pipefail
|
||||
set +u
|
||||
|
||||
RELEASE="$(rpm -E %fedora)"
|
||||
|
||||
### Add repos
|
||||
ostree remote add docker-ce https://download.docker.com/linux/fedora/docker-ce.repo
|
||||
|
||||
### Refresh repos
|
||||
rpm-ostree cleanup -m
|
||||
rpm-ostree refresh-md
|
||||
|
||||
### Install packages
|
||||
|
||||
# Packages can be installed from any enabled yum repo on the image.
|
||||
# RPMfusion repos are available by default in ublue main images
|
||||
# List of rpmfusion packages can be found here:
|
||||
# https://mirrors.rpmfusion.org/mirrorlist?path=free/fedora/updates/39/x86_64/repoview/index.html&protocol=https&redirect=1
|
||||
|
||||
# from fedora repos
|
||||
# NOTE: for now freeipa-client must be layered AFTER installation to work
|
||||
rpm-ostree install \
|
||||
usbguard \
|
||||
zsh \
|
||||
libvirt \
|
||||
virt-manager \
|
||||
autofs \
|
||||
gstreamer1-plugins-ugly-free \
|
||||
gstreamer1-plugins-bad-free \
|
||||
gstreamer1-plugins-bad-free-extras \
|
||||
gstreamer1-plugins-good \
|
||||
gstreamer1-plugins-good-extras \
|
||||
gstreamer1-plugins-base \
|
||||
gstreamer1-plugins-base-tools \
|
||||
wireguard-tools \
|
||||
trash-cli \
|
||||
git \
|
||||
git-credential-libsecret \
|
||||
gtk-murrine-engine \
|
||||
firewall-config \
|
||||
alsa-tools \
|
||||
libappstream-glib \
|
||||
htop \
|
||||
glances \
|
||||
ansible
|
||||
|
||||
# from dnf groups (gh actions will translate this to rpm-ostree install <pkgs>)
|
||||
rpm-ostree groupinstall "C Development Tools and Libraries" "Development Tools"
|
||||
|
||||
# from rpmfusion
|
||||
rpm-ostree install \
|
||||
vlc
|
||||
|
||||
# from custom repos
|
||||
rpm-ostree install \
|
||||
docker-ce \
|
||||
docker-ce-cli \
|
||||
containerd.io \
|
||||
docker-buildx-plugin \
|
||||
docker-compose-plugin
|
||||
|
||||
# TODO: Add rpm building with FPM
|
||||
|
||||
# from RPMs on Github
|
||||
# Space-separated list of repo/package strings
|
||||
repos="quexten/goldwarden"
|
||||
|
||||
# Loop through each repo/package
|
||||
for repo_package in $repos; do
|
||||
# Split the string into repo and package using parameter expansion
|
||||
repo=${repo_package%/*}
|
||||
package=${repo_package#*/}
|
||||
|
||||
# Fetch the latest release download URL for .rpm assets
|
||||
download_url=$(wget -qO- "https://api.github.com/repos/$repo/$package/releases/latest" \
|
||||
| jq -r '.assets[] | select(.name | match(".rpm")) | .browser_download_url')
|
||||
|
||||
# Download the asset as <PACKAGE>.rpm
|
||||
wget -qO "$package.rpm" "$download_url"
|
||||
|
||||
# Install the package
|
||||
rpm-ostree install "$package.rpm"
|
||||
done
|
||||
|
||||
|
||||
#### Change to System Configuration Files
|
||||
# Enable docker.service
|
||||
ln -s /etc/systemd/system/docker.service /etc/systemd/system/multi-user.target.wants/
|
||||
|
||||
# this example modifies default timeouts to prevent slow reboots from services that won't stop
|
||||
#sed -i 's/#DefaultTimeoutStopSec.*/DefaultTimeoutStopSec=15s/' /etc/systemd/user.conf
|
||||
#sed -i 's/#DefaultTimeoutStopSec.*/DefaultTimeoutStopSec=15s/' /etc/systemd/system.conf
|
||||
|
|
@ -0,0 +1,2 @@
|
|||
[org.gnome.settings-daemon.plugins.power]
|
||||
power-button-action='interactive'
|
||||
25
files/scripts/download_install_rpms.sh
Normal file
25
files/scripts/download_install_rpms.sh
Normal file
|
|
@ -0,0 +1,25 @@
|
|||
#!/bin/sh
|
||||
|
||||
set -oex pipefail
|
||||
set +u
|
||||
|
||||
# from RPMs on Github
|
||||
# Space-separated list of repo/package strings
|
||||
repos="quexten/goldwarden"
|
||||
|
||||
# Loop through each repo/package
|
||||
for repo_package in $repos; do
|
||||
# Split the string into repo and package using parameter expansion
|
||||
repo=${repo_package%/*}
|
||||
package=${repo_package#*/}
|
||||
|
||||
# Fetch the latest release download URL for .rpm assets
|
||||
download_url=$(wget -qO- "https://api.github.com/repos/$repo/$package/releases/latest" \
|
||||
| jq -r '.assets[] | select(.name | match(".rpm")) | .browser_download_url')
|
||||
|
||||
# Download the asset as <PACKAGE>.rpm
|
||||
wget -qO "$package.rpm" "$download_url"
|
||||
|
||||
# Install the package
|
||||
rpm-ostree install "$package.rpm"
|
||||
done
|
||||
1
files/system/etc/.gitkeep
Normal file
1
files/system/etc/.gitkeep
Normal file
|
|
@ -0,0 +1 @@
|
|||
|
||||
0
files/system/usr/.gitkeep
Normal file
0
files/system/usr/.gitkeep
Normal file
0
modules/.gitkeep
Normal file
0
modules/.gitkeep
Normal file
101
recipes/recipe.yml
Normal file
101
recipes/recipe.yml
Normal file
|
|
@ -0,0 +1,101 @@
|
|||
name: bazzite-badblocks-gnome
|
||||
description: badblocks's custom bazzite-gnome build
|
||||
|
||||
base-image: ghcr.io/ublue-os/bazzite-gnome
|
||||
image-version: latest
|
||||
|
||||
modules:
|
||||
- type: files
|
||||
files:
|
||||
- source: system
|
||||
destination: /
|
||||
- type: rpm-ostree
|
||||
repos:
|
||||
- https://download.docker.com/linux/fedora/docker-ce.repo
|
||||
keys:
|
||||
- https://download.docker.com/linux/fedora/gpg
|
||||
install:
|
||||
- vlc
|
||||
- usbguard
|
||||
- zsh
|
||||
- libvirt
|
||||
- virt-manager
|
||||
- autofs
|
||||
- gstreamer1-plugins-ugly-free
|
||||
- gstreamer1-plugins-bad-free
|
||||
- gstreamer1-plugins-bad-free-extras
|
||||
- gstreamer1-plugins-good
|
||||
- gstreamer1-plugins-good-extras
|
||||
- gstreamer1-plugins-base
|
||||
- gstreamer1-plugins-base-tools
|
||||
- wireguard-tools
|
||||
- trash-cli
|
||||
- git
|
||||
- git-credential-libsecret
|
||||
- gtk-murrine-engine
|
||||
- firewall-config
|
||||
- alsa-tools
|
||||
- libappstream-glib
|
||||
- htop
|
||||
- glances
|
||||
- ansible
|
||||
- docker-ce
|
||||
- docker-ce-cli
|
||||
- containerd.io
|
||||
- docker-buildx-plugin
|
||||
- docker-compose-plugin
|
||||
- type: script
|
||||
scripts:
|
||||
- download_install_rpms.sh
|
||||
- type: akmods
|
||||
install:
|
||||
- openrazer
|
||||
- xpadneo
|
||||
- xone
|
||||
- type: fonts
|
||||
fonts:
|
||||
nerd-fonts:
|
||||
- FiraCode # don't add spaces or "Nerd Font" suffix.
|
||||
- Hack
|
||||
- SourceCodePro
|
||||
- Terminus
|
||||
- JetBrainsMono
|
||||
- NerdFontsSymbolsOnly
|
||||
google-fonts:
|
||||
- Roboto
|
||||
- Open Sans
|
||||
- type: gnome-extensions
|
||||
install:
|
||||
- 3628 # ArcMenu
|
||||
- 1460 # Vitals
|
||||
- 1160 # Dash to Panel
|
||||
- 97 # Coverflow Alt-Tab
|
||||
- 779 # Clipboard Indicator
|
||||
- type: gschema-overrides
|
||||
include:
|
||||
- zz1-power-button-settings.gschema.override
|
||||
- type: default-flatpaks
|
||||
notify: true # Send notification after install/uninstall is finished
|
||||
system:
|
||||
install:
|
||||
- net.nokyan.Resources
|
||||
- org.gimp.GIMP
|
||||
- org.libreoffice.LibreOffice
|
||||
- page.codeberg.libre_menu_editor.LibreMenuEditor
|
||||
- us.zoom.Zoom
|
||||
user:
|
||||
install:
|
||||
- com.bitwarden.desktop
|
||||
- dev.zed.Zed
|
||||
- dev.goats.xivlauncher
|
||||
- com.github.zocker_160.SyncThingy
|
||||
- io.github.vikdevelop.SaveDesktop
|
||||
- md.obsidian.Obsidian
|
||||
- org.strawberrymusicplayer.strawberry
|
||||
- com.discordapp.Discord
|
||||
- type: systemd
|
||||
system:
|
||||
enabled:
|
||||
- docker.service
|
||||
- type: signing # sets up the proper policy & signing files for signed images to work fully
|
||||
|
||||
Loading…
Add table
Add a link
Reference in a new issue